- Home
- Workspace
- Installation
- Community
- Getting Started: Portal Configuration
Getting Started: Portal Configuration
Overview
Once your portal is created, you will need to customize and manage it so that it fits your needs. This can be done in the portal Settings section.
To access the Settings from any portal page, click the![]() icon at the top of the page or use the drop-down list in the top left corner and select the corresponding option.
icon at the top of the page or use the drop-down list in the top left corner and select the corresponding option.
You can perform the following operations via the portal Settings section:
Common settings
- customize the portal:
- change the portal language and set the correct time zone;
- set up the portal title displayed on the portal Sign In page;
- set an alternative URL for the portal;
- change the portal name used in your portal URL address;
- set up the team template used for the portal;
- select a color theme that suits your company brand;
- manage the portal modules:
- choose the modules and tools to show on the portal and which to hide from the portal users;
- add your own links into the portal navigation menu;
- select a default start page;
- adjust the Pricing page settings;
- use the White Label feature to replace branding elements used in the online office interface with your own ones.
Security settings
- update the Portal Access settings:
- determine the password strength used to access the portal;
- turn on two-factor authentication;
- specify mail servers allowed for user self-registration;
- adjust the IP security settings;
- set up the login settings;
- change the administrator message settings;
- set the session lifetime;
- set up the access rights for portal administrators and other users:
- change the portal owner;
- add users to the administrators list;
- restrict access to certain portal modules for users and groups;
- view the recent user login/logout activity and obtain a detailed report for six months;
- view log entries of the recent actions that users performed on the portal (such as closing and editing tasks, changing access rights, creating and deleting CRM entities, transferring documents, inviting guests, etc.), as well as download a detailed statistics file that provides data for half a year;
Data Management settings
- change the region of the server where your portal is hosted;
- create and restore the portal data backup;
- temporarily deactivate or even delete the portal forever;
Integration settings
- enable the LDAP settings;
- enable the SSO settings;
- connect third-party services;
- adjust SMTP settings for the email notifications to be sent using your own SMTP server;
Statistics settings
- see the main portal statistics: creation date, total number of users, storage space used by various modules and users, user attendance.
Common settings
The Common settings section opens by default. It allows you to adapt the appearance of the portal to your needs and choose the modules you wish to use. It includes three subsections: Customization, Modules & Tools, and White Label.
Customizing portal
The Customization subsection of the Common settings allows you to change the look and feel of your portal. You can use your own company logo, name, and text to match your organization's brand.
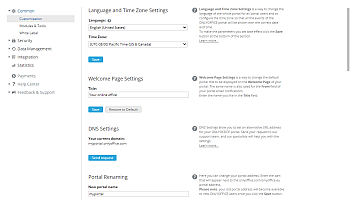
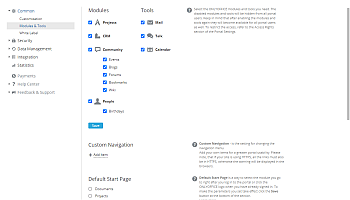
Language and time zone settings
This section allows you to change the language of the whole portal for all portal users and to configure the time zone so that all the events of the portal will be shown with the correct date and time.
To configure the Language and Time Zone settings,
- open the Language drop-down list and select the required language to display all portal pages and notifications.
This setting specifies the default portal language for new users. Each user can change the default language later by selecting the preferred one on their profile page (this setting will have a higher priority than the language selected in the Common Settings).
At present, the online office is available in 23 languages: English, German, French, Spanish, Russian, Italian, Latvian, Portuguese (Brazilian), Turkish, Greek, Polish, Czech, simplified Chinese, Ukrainian, Vietnamese, Finnish, Portuguese, Azeri, Korean, Japanese, Slovenian, Dutch, and Slovak. If your language is not available in the list, or if the translation to your language is not complete, you can contribute to the translation by sending your request at documentation@onlyoffice.com.
- set the time zone that corresponds to your location from the Time Zone drop-down list,
- click the Save button at the bottom of the section to apply the changes you made.
Welcome page settings
This section allows you to change the default title to be displayed on the Sign In page of your portal. To do that,
- enter the desired name in the Title field (e.g., your company title, its motto, etc.),
- click the Save button at the bottom of the section to apply the changes you made.
DNS settings
This section allows you to set an alternative URL for your portal. By default, your portal is registered at name.onlyoffice.com. To change it to your own domain name:
- Configure your domain name to point to the online office server by setting up the appropriate DNS records with your registry. Contact your domain registrar for instructions on how to configure DNS records. Add a DNS CNAME entry, such as, for example: team.ourcompany.com-intranet.onlyoffice.com (for the US West (Oregon) region), intranet.onlyoffice.eu (for the EU (Frankfurt) region), or intranet.onlyoffice.sg (for the Asia Pacific (Singapore) region).
- After setting up your DNS CNAME entry, click the Send request button in the DNS settings section to send your request to our support team. The https://helpdesk.onlyoffice.com/ page will open in a new browser tab. Enter the details of your request and click Submit.
In addition to setting up your custom domain, our team can also generate an SSL certificate using Let's Encrypt.
- After the request is processed, your custom domain name will be displayed in the DNS settings section.
Portal renaming
This section allows you to change the name part of your portal URL address name.onlyoffice.com so that your portal is available at newname.onlyoffice.com. Enter the desired name in the New portal name field and click the Save button.
Team template
This section allows you to name the organization (or group), its members, and their activities within your portal. To do that,
- choose one of the available presets from the Template drop-down list,
OR
- select the Custom option from the list and enter your own names in the fields below,
- click the Save button at the bottom of the section to apply the changes you made.
Color themes
This section allows you to change the default color palette of your portal interface so that it suits your company brand. To do that,
- switch between the available Color Themes to preview them: Mellow green, Dark green, Deep blue, Wild pink, Bright blue,
- select the one that suits you best,
- click the Save button to apply the selected color theme.
To return to the default color theme, click the Pure orange radio button and save your changes.
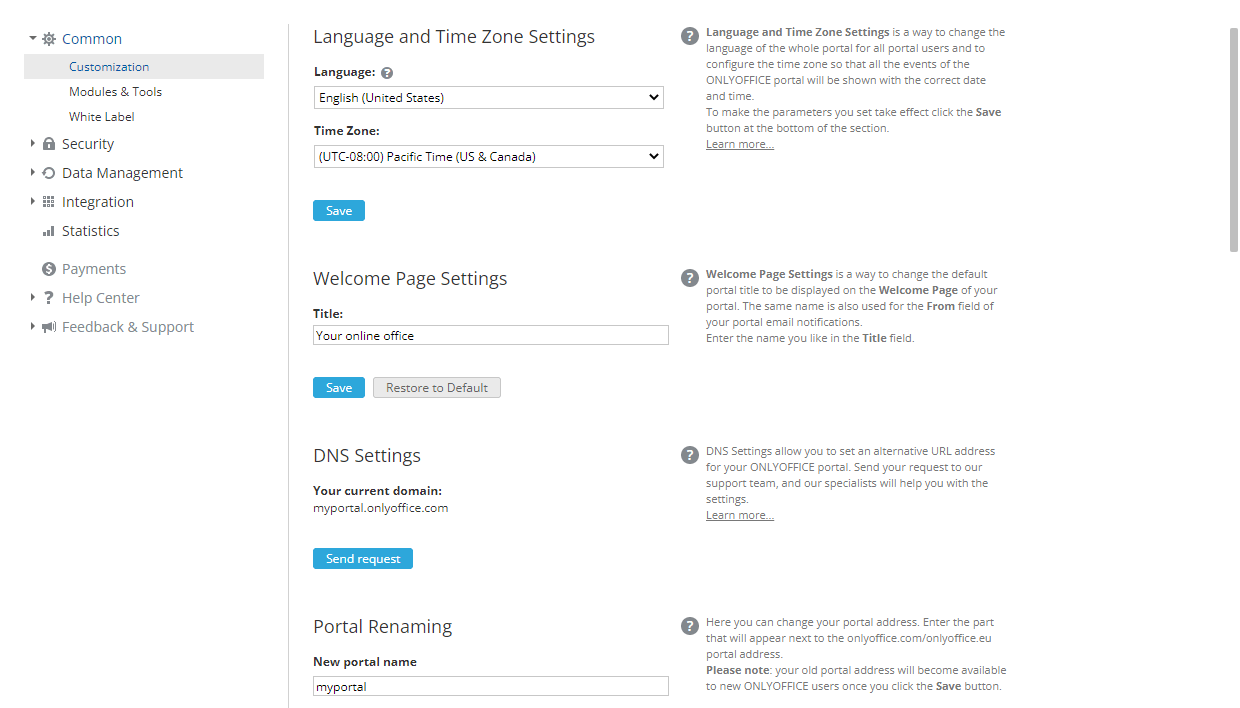
Managing portal modules
The Modules & Tools subsection of the Common settings gives you access to the list of portal modules and tools and the ability to manage them. To do that,
- leave the desired modules and tools checked, and uncheck those you do not need for your work,
Starting from v12.0, the Community module is disabled by default for newly created installations and cloud portals. It can be enabled in this section of the settings. It is also possible to manage the tools for your social network within the Community module by checking the ones you need.
- click the Save button at the bottom of the section to apply the changes you made.
The disabled modules and tools will be hidden from all portal users.
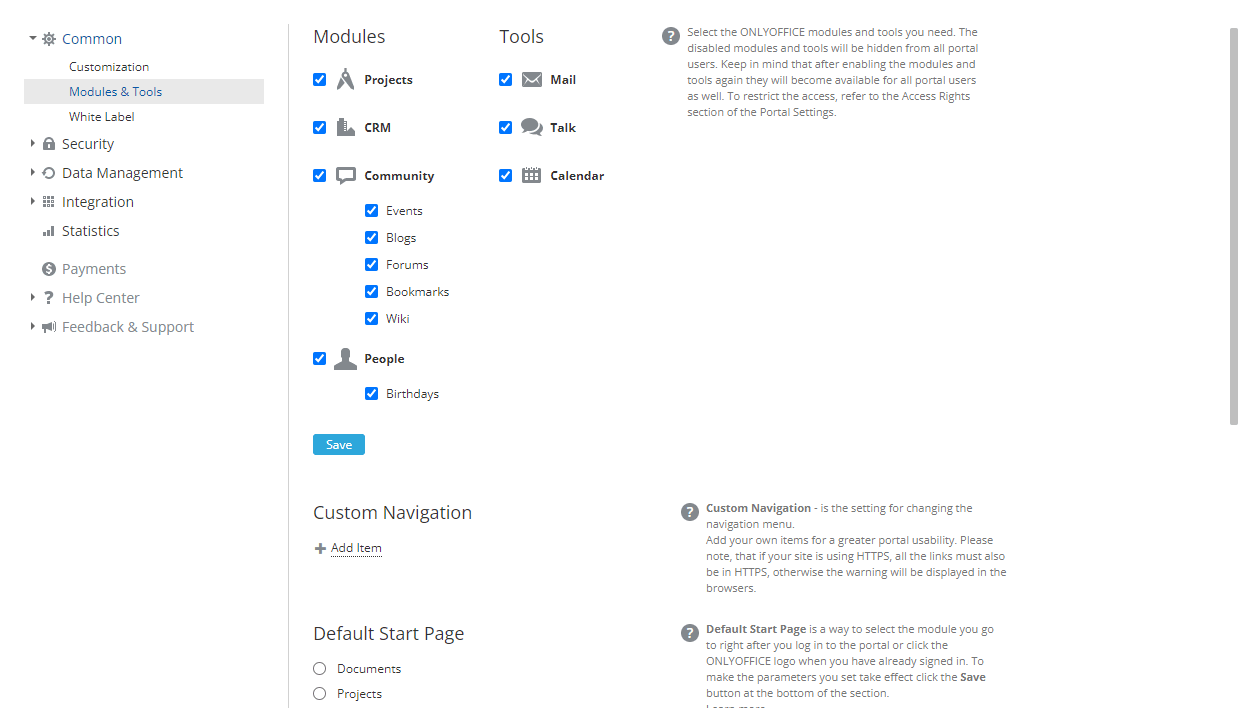
Custom navigation
This section allows you to add your own items into the portal navigation menu to improve portal usability. For example, you can add links to external websites or services
To add a new menu item:
- Click the Add Item link in the Custom Navigation section. A new window opens.


- Enter the menu item title in the Label text entry field.
- Specify the link to the necessary resource in the URL field.
Note: if your portal is using HTTPS, all the links must also be in HTTPS; otherwise, the warning will be displayed in the browsers.
- The Show in menu and Show on home page options are selected by default. You can uncheck one of them if necessary.
- Replace the default icons with your own ones. The Small icon, 16x16, will be used in the navigation menu located in the portal header. The Large icon, 100x100 will be displayed on the portal start page. Click the corresponding Change image link below to upload a new image.
- When ready, click the Save button.
The newly created navigation item will be added to the navigation menu and/or to the portal start page depending on the specified settings. It will also be displayed below the Custom Navigation title on the portal settings page. To edit the item, click the ![]() Settings icon next to it. In the Item Settings window, change the necessary parameters and click the Save button. If you want to remove the added navigation item, use the Remove Item button in the Item Settings window.
Settings icon next to it. In the Item Settings window, change the necessary parameters and click the Save button. If you want to remove the added navigation item, use the Remove Item button in the Item Settings window.
Default start page
This section allows you to choose the page you go to right after you log in to the portal or click the online office logo when you have already signed in. You can select one of the following options:
- one of the portal modules (Documents, Projects, CRM, Community, People),
- one of the tools (Mail, Talk, Calendar),
- the Feed page,
- the default Module Choice page.
Check the corresponding radio button and click the Save button at the bottom of the section to apply the changes you made.
Pricing page settings
This section allows you to determine whether the pricing page should be accessible for all portal users or for administrators only.
Check the Pricing page available for administrators only box to make this page visible for portal administrators only, and click the Save button at the bottom of the section to apply the changes you made.
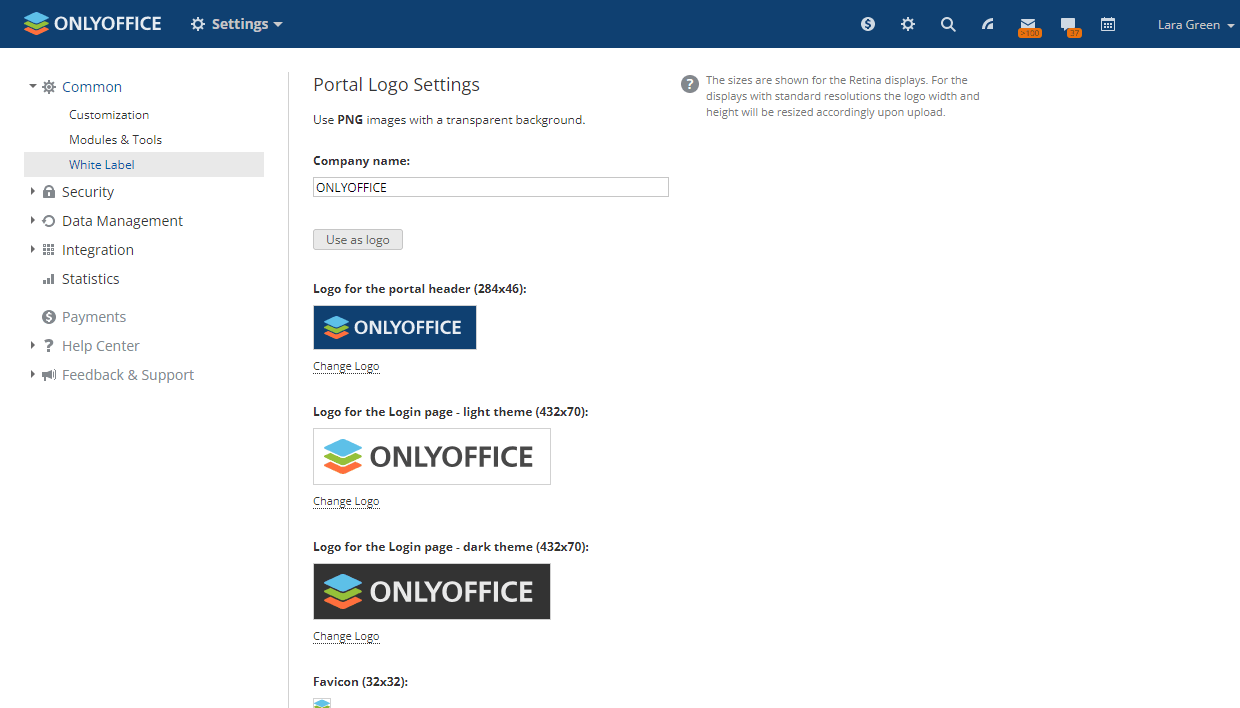
White labeling
The White Label subsection of the Common settings allows you to replace branding elements used in the online office interface with your own ones. You can use your company name in the text elements (such as tooltips, message boxes, etc.) as well as replace the default favicon and logos with your own logo. To do that,
- Enter your Company name in the text entry field to change all the titles and messages in the online office interface where the default value is used, replacing it with the one you specified. Click the Use as logo button below the entry field if you want to use your company name as a text logo (instead of an image logo) - all the logos below will change correspondingly.
- Replace all the image Logos which appear in the online office:
- Logo for the portal header (284x46) - this logo appears in the upper left corner of every portal page.
- Logo for the Login page - light theme (432x70) - this logo appears on the Sign In page of the portal, is used if the light theme is enabled.
- Logo for the Login page - dark theme (432x70) - this logo appears on the Sign In page of the portal, is used if the dark theme is enabled.
- Favicon (32x32) - this logo appears in the address bar or tab of a web browser when the portal is opened in it, or on the bookmarks panel if you've added the portal address to the bookmarks.
- Logo for the editors header (172x40) - this logo appears in the upper left corner of the online editor launched. The first, second, and third logos are used for document, spreadsheet, and presentation editors, correspondingly if the light theme is enabled; the fourth logo is used for all editors if the dark theme is enabled.
- Logo for the editors header - embedded mode (172x40) - this logo appears in the upper left corner of your portal documents embedded into web pages.
Click the Change Logo link below the logo you want to replace. In the Windows Explorer window, browse for the necessary image file and click the Open button. The image will be uploaded and displayed in the corresponding Logo field.
It is recommended that images use in the PNG format with a transparent background. To improve your logos legibility and make their outline clearly distinguishable, you also need to optimize them for use on dark or light backgrounds. The image sizes are shown for the Retina displays. For the displays with standard resolutions, the logo width and height will be resized accordingly upon upload. - click the Save button at the bottom of the section to apply the changes you made.
To return to the default settings, click the Restore to Default button.
Security settings
The Security section allows you to control access to your portal and monitor the activity of all users. It includes four subsections: Portal Access, Access Rights, Login History and Audit Trail.
Controlling portal access
The Portal Access subsection of the Security settings allows you to provide users with secure and convenient ways to access the portal.
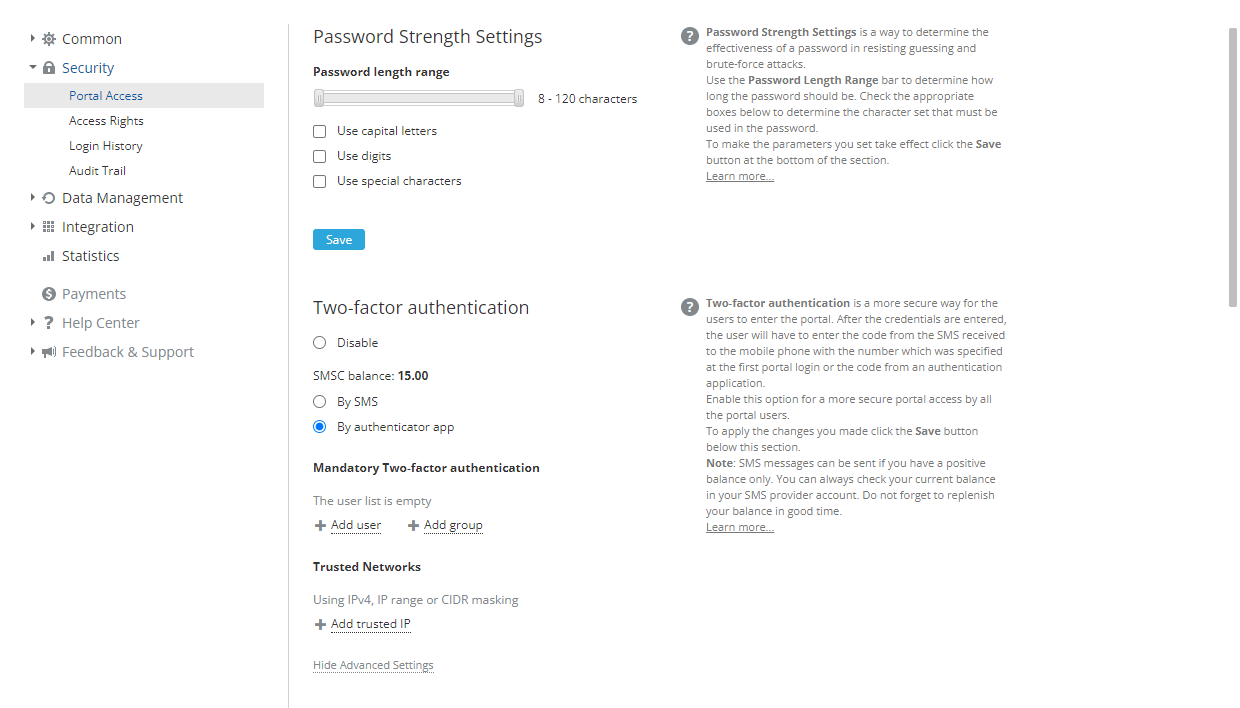
Password strength settings
This section allows you to determine password complexity (the effectiveness of a password in resisting guessing and brute-force attacks). To do that,
- use the Password length range bar to set the minimum and maximum password length,
By default, the password must be at least 8 but no more than 120 characters long.
- check the appropriate boxes below the bar to determine the character set that must be used in the password: capital letters, digits, special characters,
- click the Save button at the bottom of the section to apply the changes you made.
Two-factor authentication
This section allows you to enable two-step verification with SMS or authenticator apps that ensure more secure portal access.
If you are using the server version, you first need to connect at least one SMS provider in the Settings > Integration > Third-Party Services section so that you can enable the Two-factor authentication option.
To enable two-factor authentication with SMS,
- make sure that one of the SMS providers is connected in the Integration section,
- check the By SMS radio button under the Two-factor authentication section,
- to configure advanced options, click Show Advanced Settings and set the necessary options:
- in the Mandatory Two-factor authentication section, you can add users or groups for which two-factor verification will be performed even if the user comes from a trusted IP. For other users who are not included into the Trusted Networks list, two-factor verification is performed as usual.
- in the Trusted Networks section, you can add trusted IP addresses for which two-factor verification will not be performed. Specify separate IP addresses in the IPv4 format (x.x.x.x, where # is a numeric value from 0 to 255), or set an IP address range by entering the starting and ending IP addresses of the range in the x.x.x.x-x.x.x.x format, or use CIDR masking in the x.x.x.x/# format.
- click the Save button at the bottom of the section to apply the changes you made.
When two-factor authentication with SMS is enabled, a user can access the portal data after entering their regular email and password or signing in via a social media account and typing in a six-digit verification code received via SMS.
The SMS messages are sent to the user's primary mobile phone, which is specified during the first portal login via two-factor authentication and later can be changed on the user profile page. A verification code can be resent by clicking the Send code again button, but no more often than 5 times per 5 minutes. The sent code is valid for 10 minutes.
SMS messages can be sent if you have a positive balance only. You can always check your current balance in your SMS provider account. Keep your account balance up to date so your service isn't interrupted.
To enable two-factor authentication with an authenticator app,
- check the By authenticator app radio button under the Two-factor authentication section,
- to configure advanced options, click Show Advanced Settings and set the necessary options:
- in the Mandatory Two-factor authentication section, you can add users or groups for which two-factor verification will be performed,
- in the Trusted Networks section, you can add trusted IP addresses for which two-factor verification will not be performed. Specify separate IP addresses in the IPv4 format (x.x.x.x, where # is a numeric value from 0 to 255), or set an IP address range by entering the starting and ending IP addresses of the range in the x.x.x.x-x.x.x.x format, or use CIDR masking in the x.x.x.x/# format.
- click the Save button at the bottom of the section to apply the changes you made.
When two-factor authentication with an authenticator app is enabled, a user can access the portal data after entering their regular email and password or signing in via a social media account and typing in a six-digit verification code or a backup code generated by the authenticator app.
To access the portal for the first time after enabling two-factor authentication:
- Enter your regular credentials to access the portal. The QR code and your secret key are displayed on your portal login confirmation page.
- Install an authenticator app on your mobile device. You can use Google Authenticator for Android and iOS or Authenticator for Windows Phone.
- Open the authenticator app on your mobile device and configure it in one of the following ways:
- Scan the QR code displayed in the browser, or
- Manually enter your secret key displayed in the browser.
- On your portal login confirmation page, enter a 6-digit code generated by your application.
- Click the Connect app button.
To learn more on how to use two-factor authentication on your portal, refer to the Two-factor authentication guide.
Trusted mail domain settings
This section allows you to specify the mail servers used for user self-registration on your portal. By default, this option is disabled. To enable it,
- check the Custom domains radio button,
- enter the trusted mail server in the field that appears below,
- check the Add users as guests box if you wish the added users to get the view-only permissions,
- click the Save button at the bottom of the section to apply the changes you made.
To add more mail servers, use the Add trusted domain link. To delete a server added by mistake, click the corresponding ![]() icon to the right of the field.
icon to the right of the field.
After that, any user who has an account at a specified mail server will be able to register on their own by clicking the Click here to join link on the Sign In page and entering the email address. An invitation email with a link to the portal will be sent to the specified email address. To sign in, the user will need to follow the link provided in the email, enter a password, and confirm it.
To disable this option again, check the Disabled radio button.
IP security settings
This section allows you to prevent unwanted visitors from accessing your portal by allowing access to the portal from trusted networks only. If a user attempts to log in to your portal from any IP address except those you specify, this login attempt will be blocked. To restrict access to your portal based on the IP addresses,
- check the Enable radio button;
- click the Add allowed IP address link in the necessary section:
- For all users - this section allows you to set rules that are applied to all users, including full access administrators.
- For full access administrators - this section allows you to set additional rules which are applied to full access administrators only.
- in the entry field that appears, specify a single IP address in the IPv4 format (x.x.x.x, where # is a numeric value from 0 to 255), or set an IP address range by entering the starting and ending IP addresses of the range in the x.x.x.x-x.x.x.x format, or use CIDR masking in the x.x.x.x/# format;
You can find the information on your portal visitors IP addresses in the Login History subsection of the Security settings by clicking the Download and open report button.
- in the same way, add as many trusted IP addresses as you need;
- click the Save button at the bottom of the section.
If necessary, you can delete the added IP addresses by clicking the corresponding ![]() icon to the right of the IP address. To disable this option again, check the Disable radio button and click the Save button.
icon to the right of the IP address. To disable this option again, check the Disable radio button and click the Save button.
Login settings
This section allows you to protect the portal against brute-force attacks.
- in the Number of attempts field, set up the limit of unsuccessful login attempts by the user;
- in the Blocking time (sec) field, set up the time interval for blocking new login attempts;
- in the Check period (sec) field, set up the time interval for counting unsuccessful login attempts.
When the specified limit of unsuccessful login attempts is reached, attempts coming from the associated IP address will be banned (or, in the SaaS version, captcha will be requested) for the chosen period of time.
By default, this feature is disabled in the server version. If you want to use it, it is necessary to enable the feature in the configuration file. To learn more, refer to the Recaptcha configuration guide.
Administrator message settings
This section allows you to display the contact form on the Sign In page so that people can send a message to the portal administrator in case they have troubles while accessing the portal.
To enable it, check the corresponding radio button and click the Save button at the bottom of the section to apply the changes you made.
Session lifetime
This section allows you to set a time limit (in minutes) during which users will be required to re-enter their credentials to access the portal.
To set a session lifetime, check the Enable radio button, enter the necessary time value measured in minutes in the Lifetime field that appears, and click the Save button at the bottom of the section to apply the changes you made. After that, all the users will be logged out from the portal.
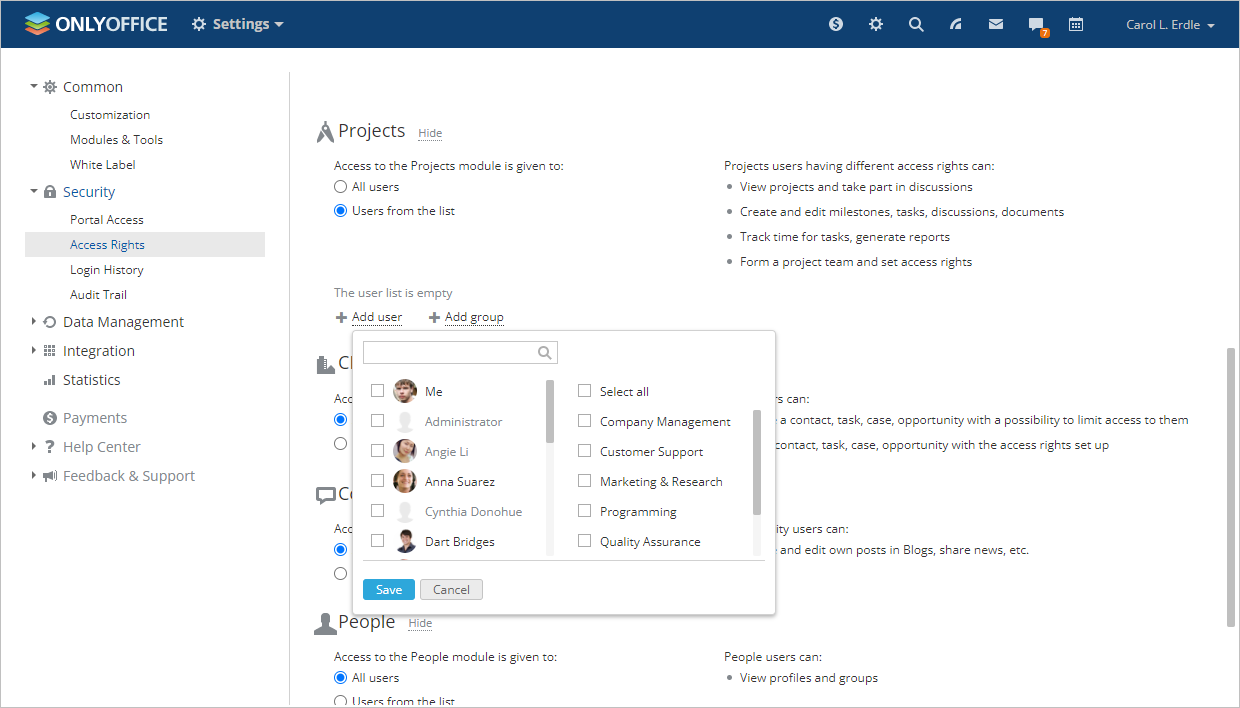
Managing access rights
The Access Rights subsection of the Security settings is used to change the portal owner, grant administrator privileges to users, and restrict access to certain portal modules for users and groups.
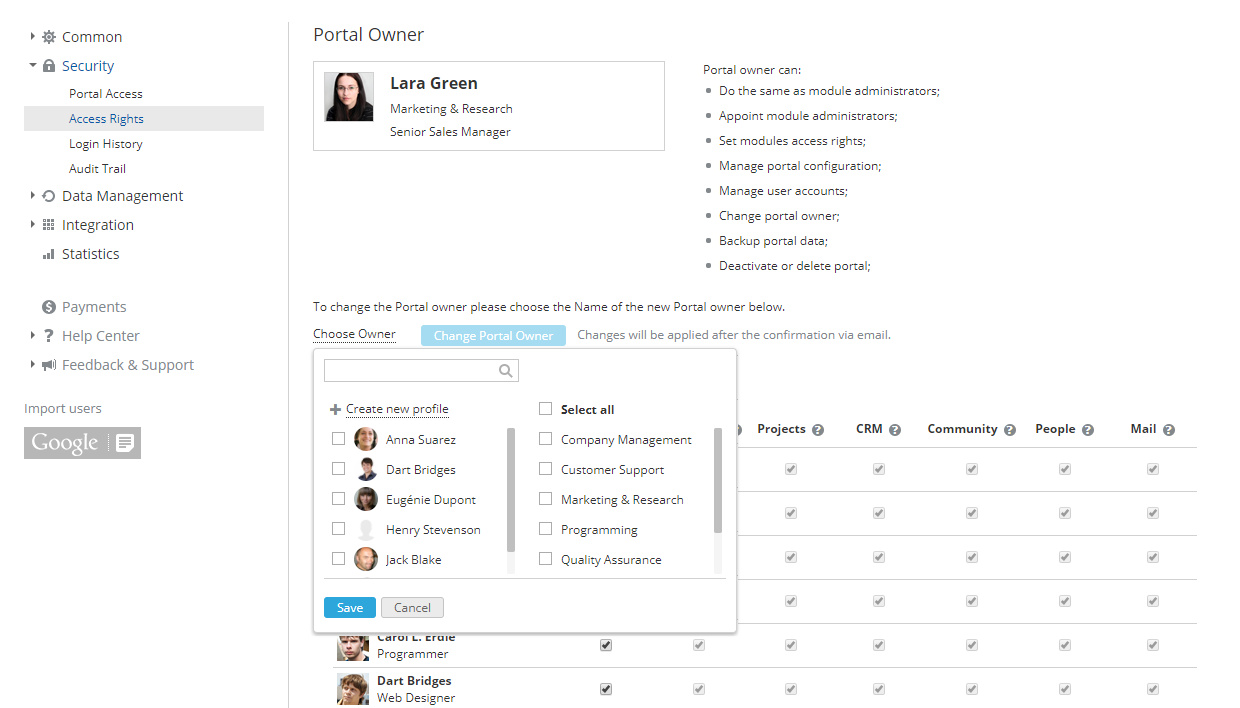
Changing portal owner
If the portal owner wants to appoint another portal member to this position, they need to:
- click the Choose Owner link under the photo in the Portal Owner section,
- select a person from the drop-down list,
- click the Change Portal Owner button,
- check the mail box and follow the confirmation link sent in the email message.

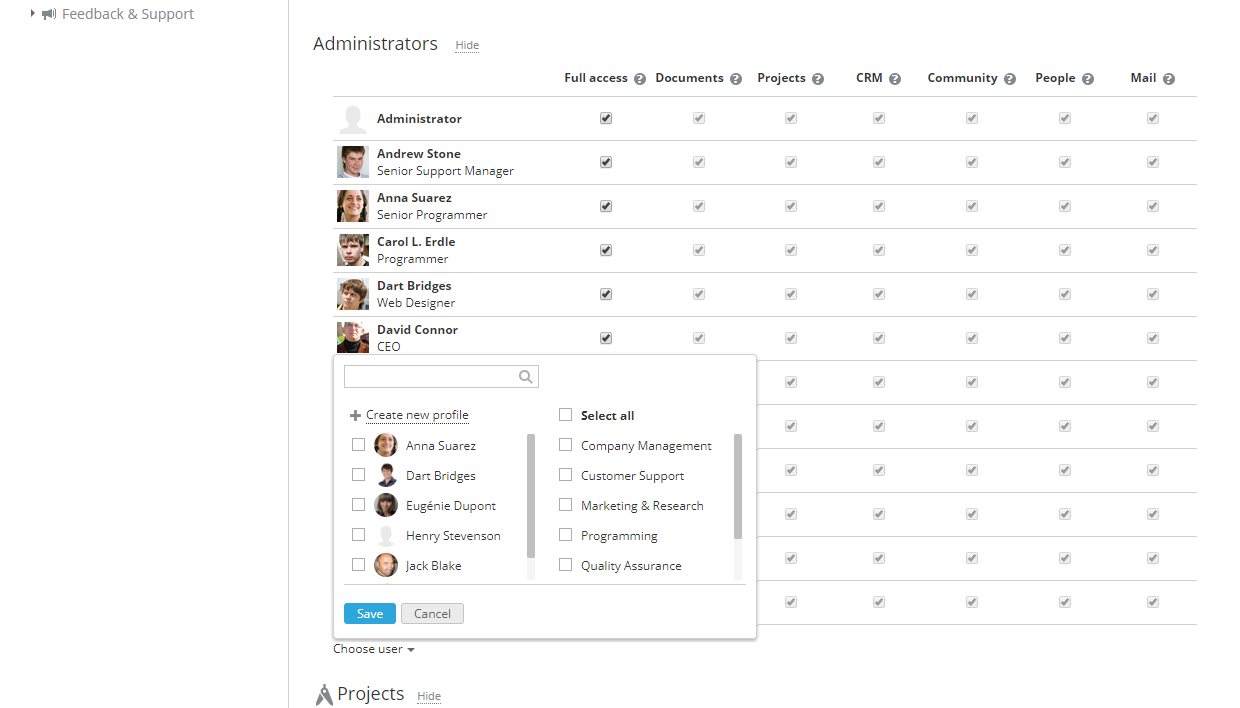
Adding administrators
The portal owner or full-access administrators can grant administrator privileges to users only (not to guests). To do that, follow these steps:
- click the Show link next to the Administrators section,
- click the Choose user link under the list of administrators,
- select a person or several persons at once from the existing users/guests or create a new administrator right here by clicking the Create new profile link,
- click the Save button,
- the selected person(s) will get the maximum access to all portal modules by default; to limit it, uncheck the Full Access box first and then the boxes corresponding to the modules you do not want to grant administrator access to.
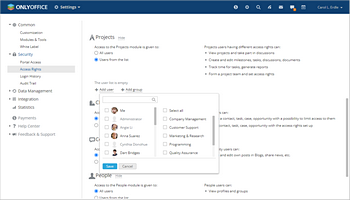
Restricting access to portal modules
The portal owner or full-access administrators can restrict access to certain portal modules for some users or groups.
To restrict access to a portal module,
- find the necessary module section below the Administrators list,
- check the Users from list radio button,
- select the users you wish to grant access to,
To do that, use one of the available options:
- use the Add user link if you wish to grant access to one or more people;
- use the Add group link if you wish to grant access to all portal users, or to one or more groups.
Tracking login history
The Login History subsection of the Security settings is used to monitor the latest user login activity, including successful logins and failed attempts, with an indication of reasons.
This page displays only the last 20 records. Each record shows which action took place, who performed it, and when the event occurred. You can also set the period during which the data is stored. By default, it is set to 180 days.
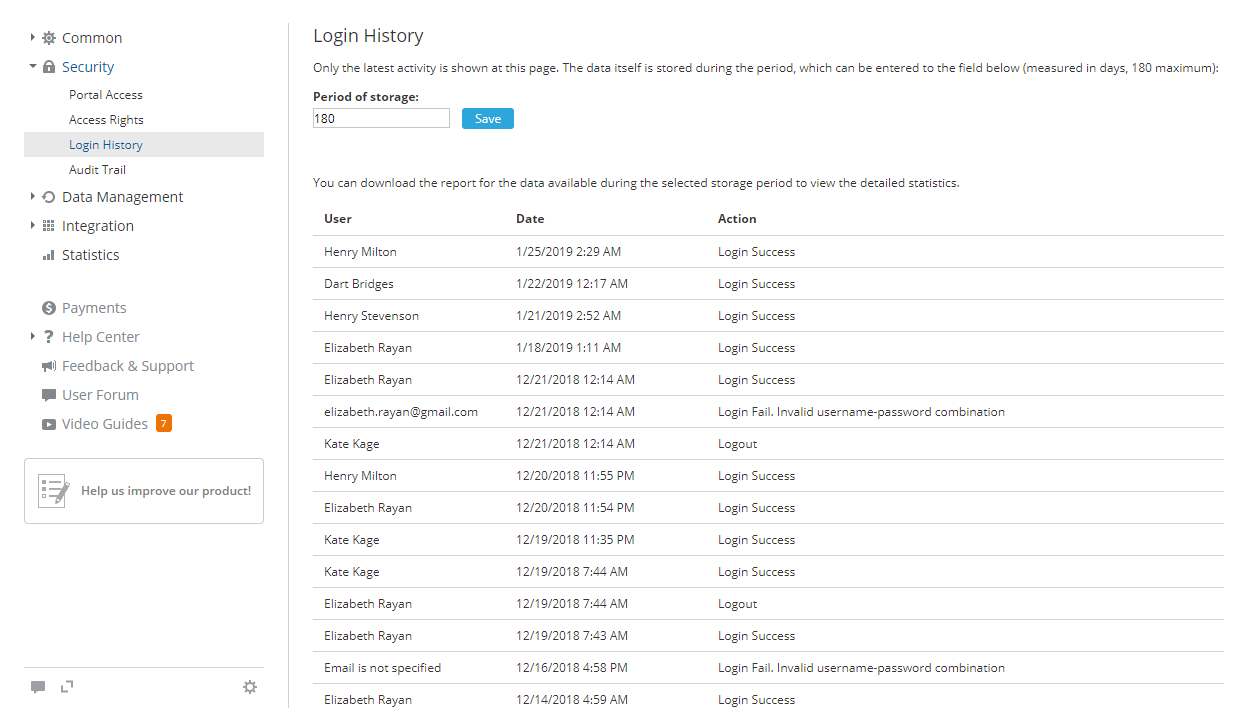
To view the detailed statistics for the past six months, click the Download and open report button. The report will open in a .csv file (LoginHistory_ReportStartDate-EndDate.csv).
The login history report includes the following details: user IP address, Browser and Platform that were used when the registered event occurred, Date and time of the event, name of the User who made an attempt to log in or log out, portal Page where the action has been performed, specific Action (for example, Login Fail. Associated Social Account Not Found).
The records are sorted chronologically in descending order, but you can easily sort and filter the data by any parameter or use the search tool to quickly find a specific record.
In the Online Users section, you can also view the list of the users who are currently logged in as well as each online user session duration.
Receiving audit trail data
The Audit Trail subsection of the Security settings allows you to browse through the list of the latest changes (creation, modification, deletion, etc.) made by users to the entities (tasks, opportunities, files, etc.) on your portal.
This page displays only the last 20 records. Each record shows which action took place, who performed it, and when the event occurred. You can also set the period during which the data is stored. By default, it is set to 180 days.
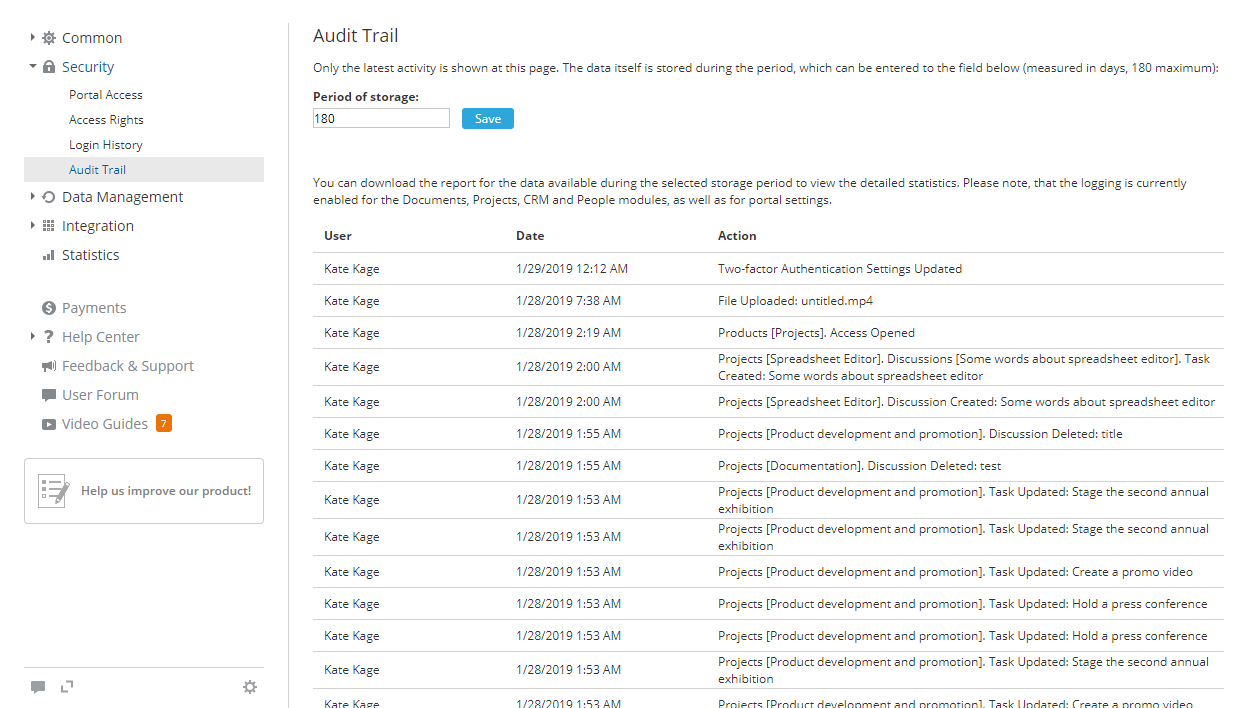
To view the detailed statistics for the latest half year, click the Download and open report button. The report will open in a .csv file (AuditTrail_ReportStartDate-EndDate.csv).
The audit trail report includes the following details: user IP address, Browser and Platform which were used when the registered event occurred, Date and time of the event, name of the User who performed the operation, portal Page where the action has been performed, generic Action Type (for example, download, attach, updated access), specific Action (for example, Projects [Product development and promotion]. Tasks [Distribute coupons]. Status Updated: Closed), Product and Module that the changed entity is referred to.
The records are sorted chronologically in descending order, but you can easily sort and filter the data by any parameter or use the search tool to quickly find a specific record.
Data management settings
The Data Management settings section allows you to protect your data, manage backups, and control your portal status. It includes three subsections: Migration, Backup and Deactivating/Deleting Portal.
Changing portal region
The Migration subsection of the Data Management settings section allows you to change the location of the server where your portal is hosted. The closer the server region is to your geographical location, the faster your portal will respond.
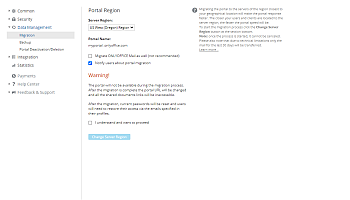

At present, you can select between three server regions: EU (Frankfurt) Region, US West (Oregon) Region, and Asia Pacific (Singapore). To migrate from one region to another one,
- select the necessary Server Region from the drop-down list,
- check the Migrate Mail as well box if you wish to transfer your mail as well,
The Mail migration may considerably increase the migration time. In addition, only the mail for the last 30 days will be transferred. Therefore, it is recommended to reconfigure your mail account after the migration is complete.
- notify users about portal migration, leaving the corresponding box checked,
- click the Change Server Region button to start the migration process.
The migration process may take some time depending on your portal data amount. During this process, the portal will not be available. Once the migration is complete, you will receive the email with the new portal address.
After the migration, current passwords will be reset, and users will need to restore their access. Users will receive notifications to the emails specified in their profiles and will be able to use the Set password button in this message to specify the password that will be used for signing in.
Creating backup
The Backup subsection of the Data Management settings allows you to backup your portal data.
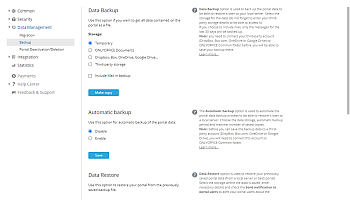
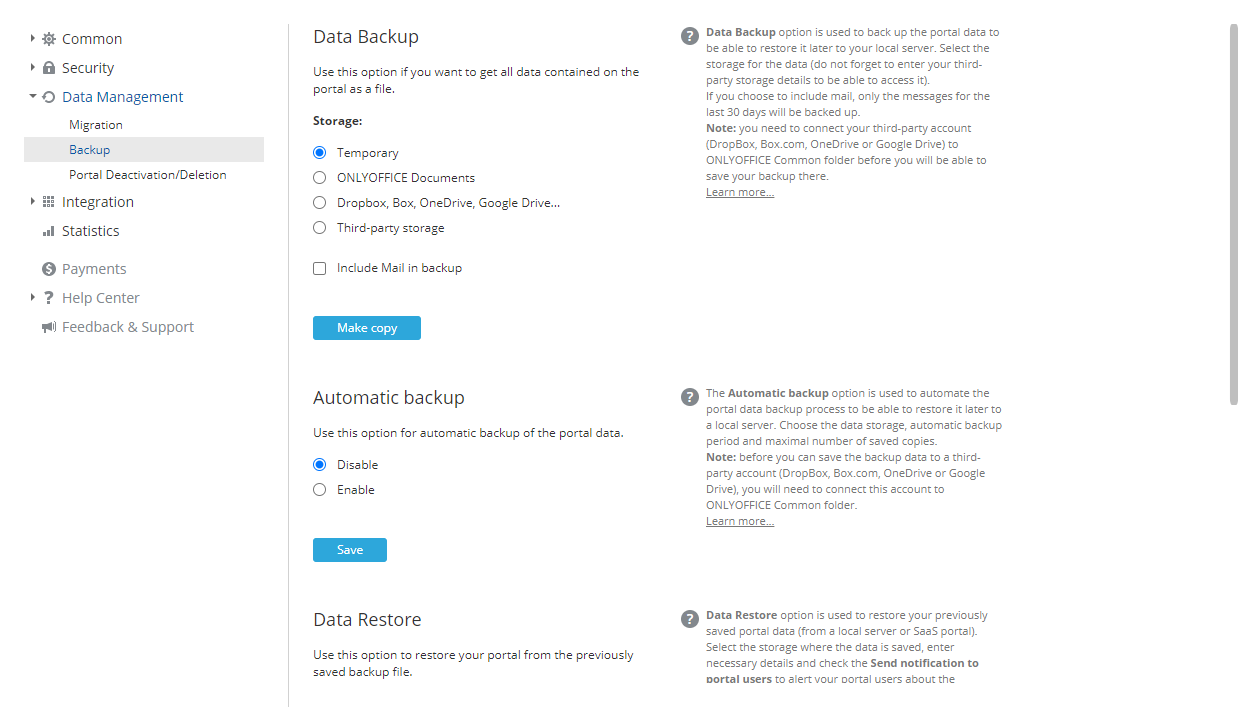
Data backup
To create your portal data backup manually, use the Data Backup section:
- select the desired Storage for your backup files:
- select the Temporary radio button if you wish to download the backup to your local drive when the backup process is over. You'll be able to do that by using the link that appears below.
- select the Documents radio button and click the Choose button next to the field that appears below. The Select folder window will open. Set a folder in the Common Documents section where you wish to store your backup and click the OK button.
- select the DropBox, Box, OneDrive, Google Drive radio button and click the Choose button next to the field that appears below. The Select folder window will open. Set a third-party resource directory located in the Common Documents section where you wish to store your backup and click the OK button.
The third-party resource must be previously connected to the Documents module as well as be shared and placed into the Common Documents section. Otherwise, the Dropbox, Box, OneDrive, Google Drive options will be disabled.
- select the Third-Party Storage radio button and choose one of the available services from the list: Amazon AWS S3 (Amazon Simple Storage Service), Google Cloud Storage, Rackspace Cloud Storage or Selectel Cloud Storage. Enter the necessary data to access the selected third-party storage in the fields below.
The corresponding service must be previously connected in the Integration section. Otherwise, the following settings will be disabled.
- For the Amazon AWS S3 service, the following fields are available:
- Bucket - a unique Amazon bucket name, e.g., my-new-test-bucket-12345.
- Region - an AWS region where your Amazon bucket resides, e.g., us-east-2.
- Service Url - this is an optional property; change it only if you want to try a different service endpoint. Leave this field empty to use the default value.
- Force Path Style - when true, requests will always use path style addressing. Leave this field empty, as the Service Url property is not specified.
- Use Http - if this property is set to true, the client attempts to use the HTTP protocol if the target endpoint supports it. By default, this property is set to false. Set it to true or leave this field empty to use the default value.
- Server Side Encryption Method - the server-side encryption algorithm used when storing this object in S3. The possible values are:
- None
- Server-Side Encryption - SSE-S3 (your assets will be encrypted with strong AES-256 GCM keys, one separate key for each object. The keys themselves are encrypted with a rotating root key for additional protection) or SSE-KMS (your assets will be encrypted with a versatile encryption mechanism. Like SSE-S3, it relies on a strong AES-256 encryption method but provides a more complex and flexible model, offering separate permissions for a KMS key, an audit trail feature, and the ability to create unique custom keys). For SSE-KMS, you can choose Managed CMK - Default AWS managed CMK or Customer managed CMK. When the Customer managed CMK option is selected, you need to specify the KMS Key Id.
- Client-Side Encryption - when this option is selected, you need to specify the KMS Key Id.
- For the Google Cloud Storage service, the following field is available: Bucket.
- For the Rackspace Cloud Storage service, the following fields are available: Public container, Private container and Region.
- For the Selectel Cloud Storage service, the following fields are available: Private container and Public container.
- For the Amazon AWS S3 service, the following fields are available:
If you select the Documents or Dropbox, Box, OneDrive, Google Drive option, the backup file size affects the overall disk space used on your portal. - check the Include Mail in backup box if you want to backup the Mail data as well. This increases the backup process time and backup file size, but if this option is unchecked, the Mail data will be lost after restoring, and you will need to connect accounts again.
- click the Make copy button.
Once the backup process is completed, you will find the backup .tar.gz file (portal-name_date_time.tar.gz) in the specified folder. If you've selected the Temporary storage, the link to download the created backup will be available for 24 hours.
To automate the backup process, use the Automatic backup section:
- check the Enable radio button.
- select the desired Storage for your backup files (the available options are the same as those described above, except for the Temporary storage, which is only available in the Data Backup section).
- check the Include Mail in backup box if you want to backup the Mail data as well.
- specify the time interval at which backups should be created: Every day with an indication of the necessary time of the day, Every week with an indication of the day of the week and time of the day, or Every month with an indication of the necessary day of the month and time of the day.
- set The maximal number of backup copies to be stored by selecting the desired value from the corresponding drop-down list.
- click the Save button.
Backups will be created automatically with the specified periodicity.
Data restore
To restore your portal data from a previously created backup file (for ONLYOFFICE Workspace Cloud 11.5 or later),
- Select the Source where the backup is stored.
- select the ONLYOFFICE Documents option and click the Choose button below. In the Select file window, choose the backup file stored in the Common folder and click OK.
- select the DropBox, Box.com, OneDrive, Google Drive option (third-party services connected to the Documents module, including services connected via the WebDAV protocol) and click the Choose button below. In the Select file window, choose the backup file stored in the third-party resource directory and click OK.
- select the Third-Party Storage option, choose the necessary third-party storage previously connected in the Integration section, and enter the data required to access the chosen storage.
- select the Computer file option, click the Choose button below, and browse for the backup file stored on your local drive.
Instead of selecting a backup file from a certain Source, you can click the Show the backup list link below the Choose field to select the backup file from the backup history (if a backup file was deleted manually from the storage, it will not be available in the list). Click the Restore link next to the backup file. To delete a backup file from the list, click the
 icon.
icon.
- Leave the Send notification about portal restoring to users box checked to notify your portal users;
- Click the Restore button.
After restoring the backup in the cloud version, current passwords will be reset, and users will need to restore their access via the email addresses specified in their profiles by specifying the password that will be used for signing in.
For more tips, you can refer to this article for the Cloud version and the Server version.
Deactivating/deleting portal
The Deactivating/Deleting Portal subsection of the Data Management settings allows you to temporarily deactivate or permanently delete your portal.
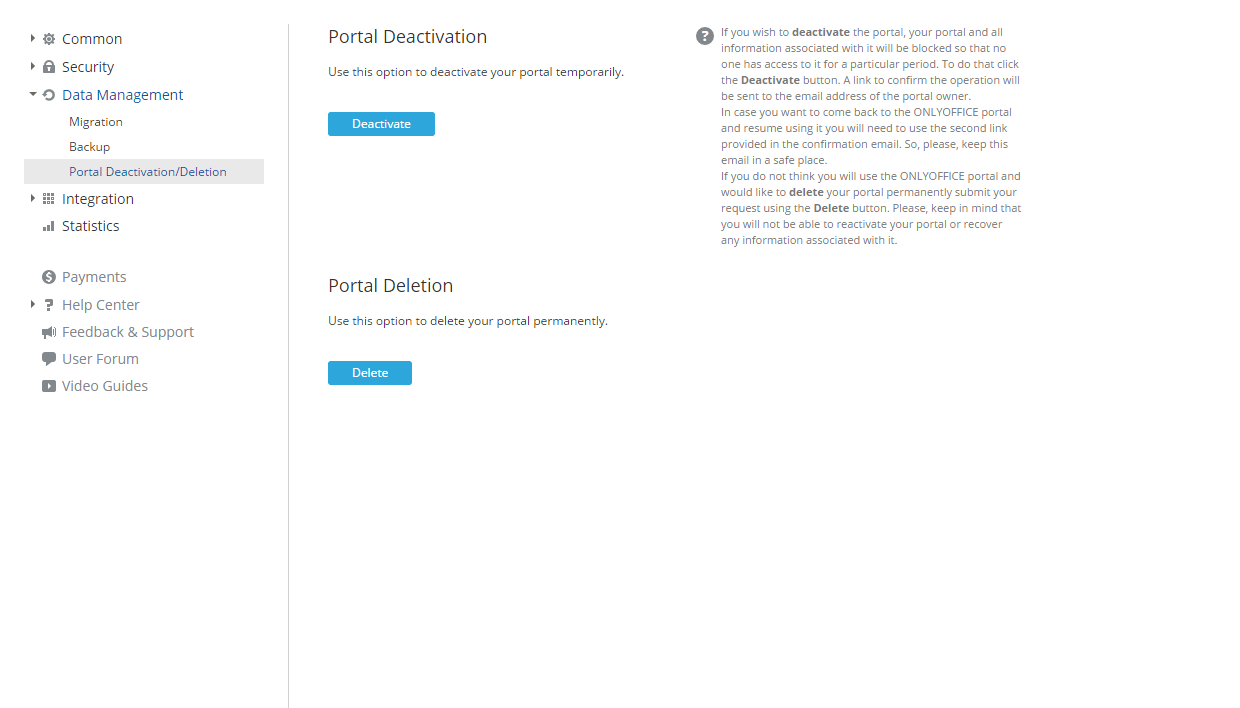
Portal deactivation
If you decide not to use the portal for some temporary reasons, deactivate it. To do that,
- click the Deactivate button.
- a link to confirm the operation will be sent to the email address of the portal owner. Follow the link to confirm the operation.
After that, your portal and all information associated with it will be blocked so that no one has access to it during a particular period.
You will be able to reactivate your portal at any moment. To come back to the portal and start using it again, use the second link provided in the confirmation email. Keep this email in a safe place.
Portal deletion
"If you no longer need the portal and want to delete it permanently,
- click the Delete button to submit your request.
- a link to confirm the operation will be sent to the email address of the portal owner. Follow the link to confirm the operation.
All the data stored on your portal as well as your registration details will be deleted. You will not be able to reactivate your portal or recover any information associated with it.
Integration settings
The Integration section is used to enable the LDAP and SSO settings, integrate your portal with third-party services, and adjust the SMTP settings.
LDAP settings
When using ONLYOFFICE Workspace, creating accounts for over 50 employees can be time‑consuming. The LDAP Settings option allows you to import users and groups from an LDAP Server in minutes. New users sign in with their existing LDAP credentials, eliminating the need for new passwords or logins.
Fill out the required fields and click Save.
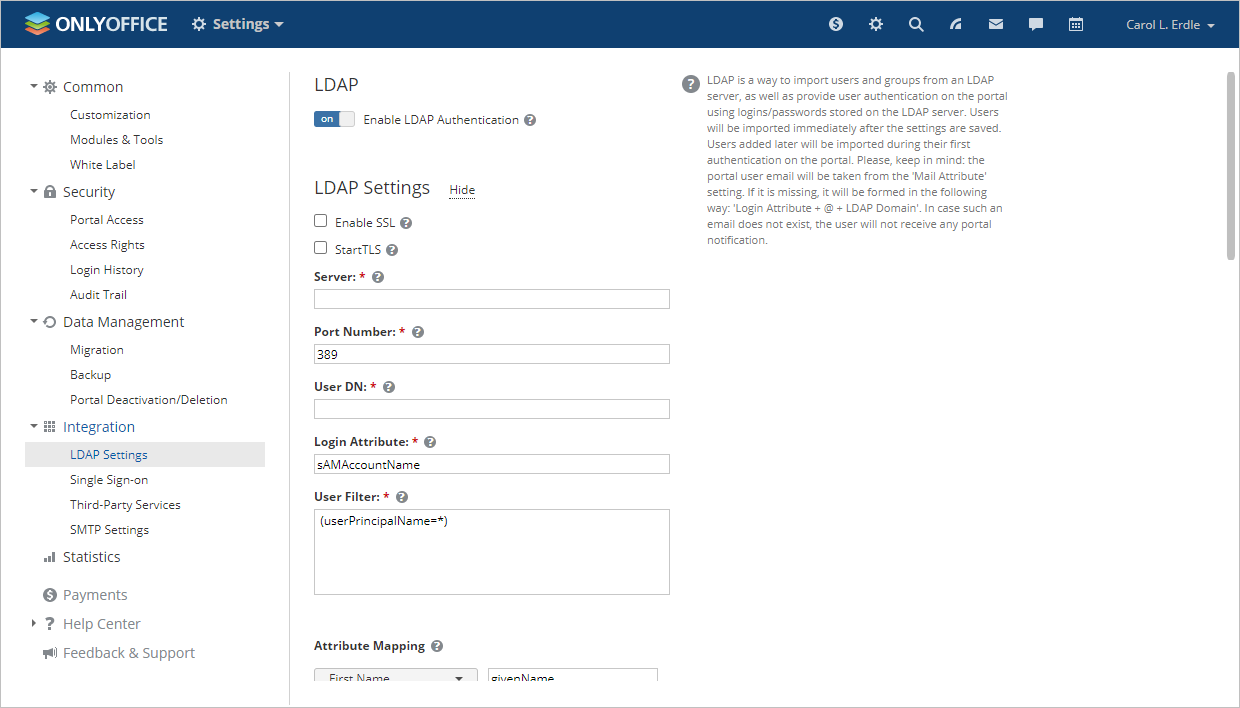
For more detailed information on each field and corresponding values, please refer to the following instructions for the SaaS version and the Server version.
Single sign-on settings
The Single Sign-on section allows you to enable/disable third-party authentication using SAML, thereby providing users with a quicker, easier, and more secure way to access the portal.
Generally, the Single Sign-on technology allows users to sign in only once and then get access to multiple authorized (i.e., integrated with an Identity Provider) applications/services without having to enter their credentials each time they access a different application.
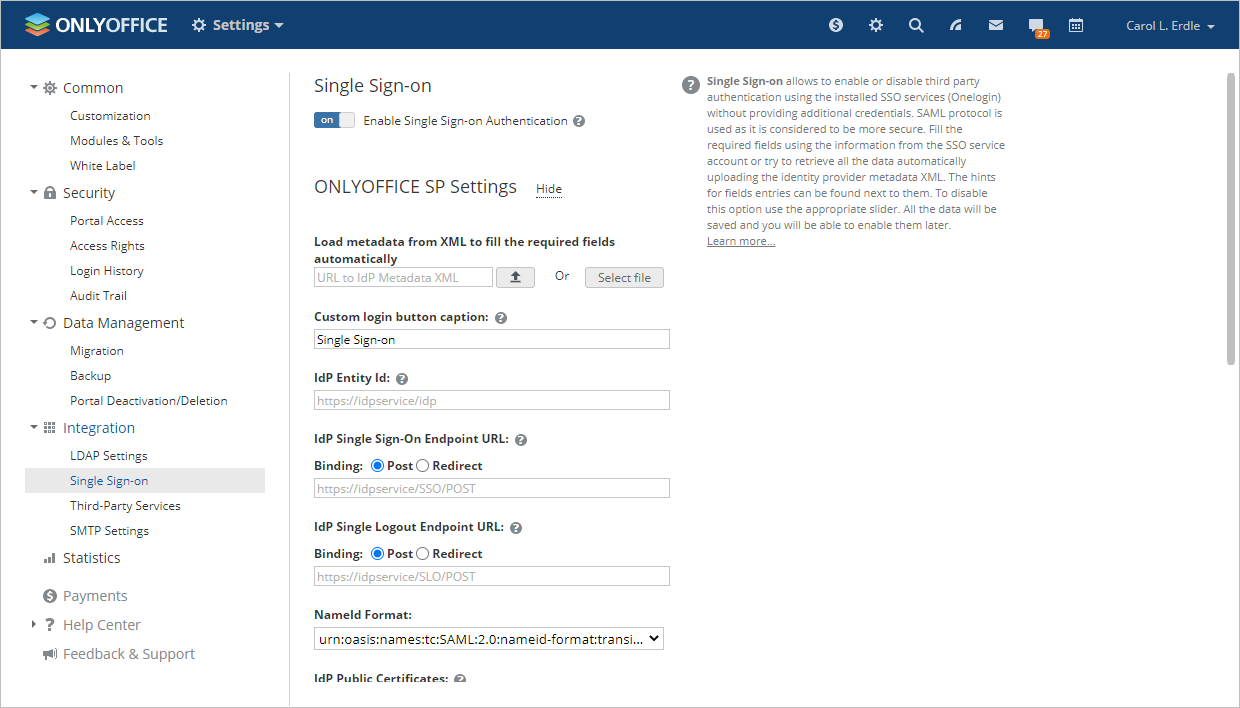
To learn more about configuring SSO, read the corresponding articles for the SaaS version and the Server version.
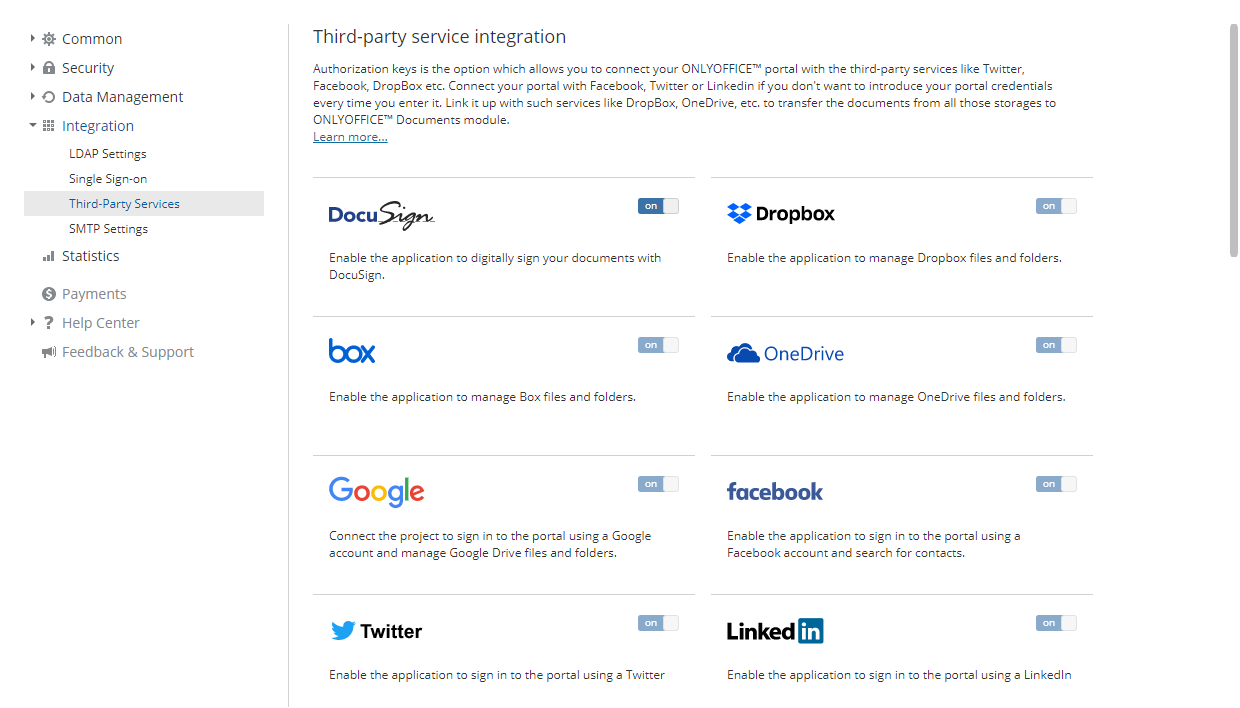
Third-party service integration
If you use the SaaS version, the authorization key parameters for most services, such as Facebook, Twitter, Google, LinkedIn, Box, Dropbox, OneDrive, Bitly, Firebase, and Yahoo are set up automatically, so the corresponding switchers are disabled. You can connect your Facebook/Google/LinkedIn/Twitter account on your profile page right away or follow the appropriate instructions to learn how to connect third-party services within the Documents module.
In the SaaS version, you can connect the following services on the Third-Party Services page:
- DocuSign - to send a file from the Documents module for electronic signature to your portal employees.
- Twilio - to be able to call your CRM contacts from a web browser. You can also use Twilio to enable two-factor authentication.
- Amazon AWS S3, Google Cloud Storage, Rackspace Cloud Storage or Selectel Cloud Storage - to backup and store data from your portal.
For more details on the third-party service integration, please refer to our instructions.
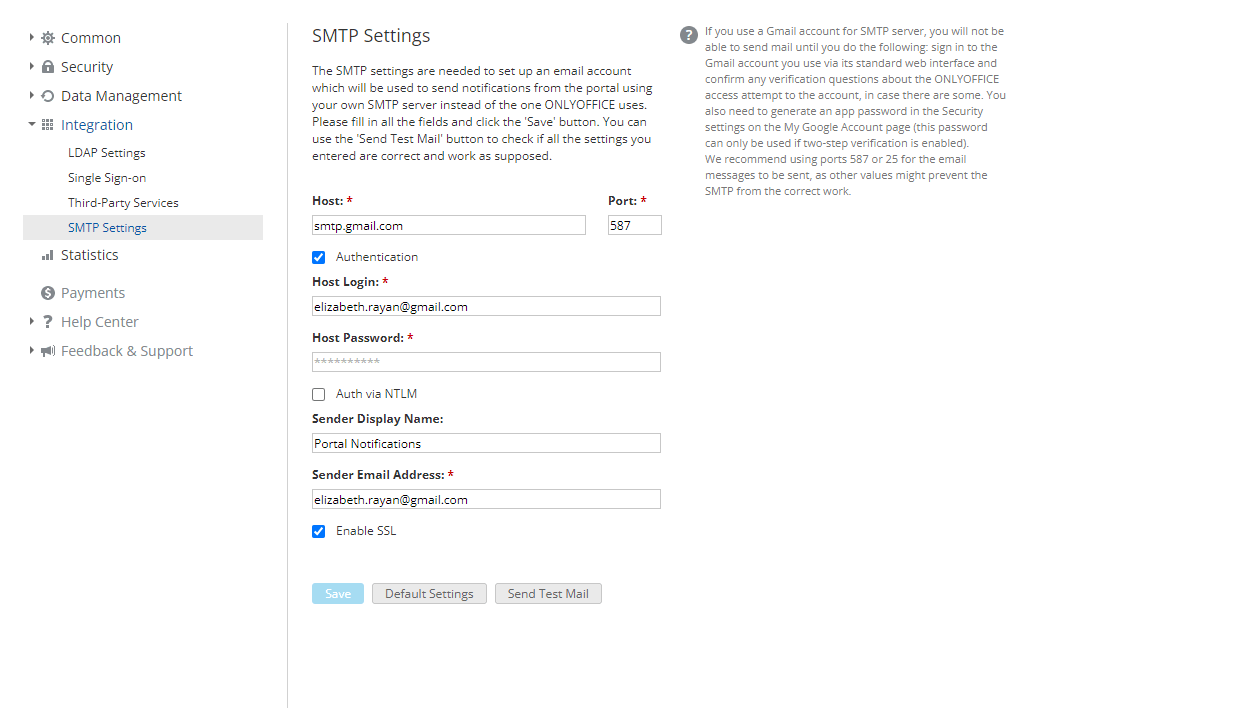
Adjusting SMTP settings
The SMTP Settings subsection allows you to configure your portal so that the email notifications be sent using your own SMTP server. To do that,
- in the Host field, specify the domain name of the SMTP server you use;
- in the Port field, specify the SMTP port number. It is recommended to use port 587 or 25.
- check the Authentication box if the SMTP server requires authentication;
- in the Host Login and Host Password fields, specify the login and password you use to access the SMTP server;
- check the Auth via NTLM box to be able to login using SaslMechanismNtlm;
- in the Sender Display Name field, specify the name of the sender, which will be displayed in the From: field;
- in the Sender Email Address field, specify the email address of the sender;
- check the Enable SSL box to enable encrypted connections;
- click the Save button.
To verify whether the specified settings are correct, click the Send Test Mail button. If the settings are specified correctly, you will receive the SMTP Test Message to the email address specified in your user profile on the portal.
For more details, please refer to SMTP configuration guide.
Statistics settings
The Statistics section is used to present and summarise your portal data for analysis and management.
Viewing portal statistics
Here you can view the following information:
- your portal creation date,
- the number of active users registered on your portal,
- the storage space allowed for the selected pricing plan (for the SaaS solution),
- the base memory quota for all new users and the list of users with the amount of space used in each module (for the SaaS solution),
- the total storage space used,
You can also view the storage space used by each portal module or tool.
- the total number of visits per day,
By default, the Usage Graph shows data for the last 3 months. You can change the period by selecting one of the available options: last week, last month, or for a period, setting the start and end date in the corresponding fields.
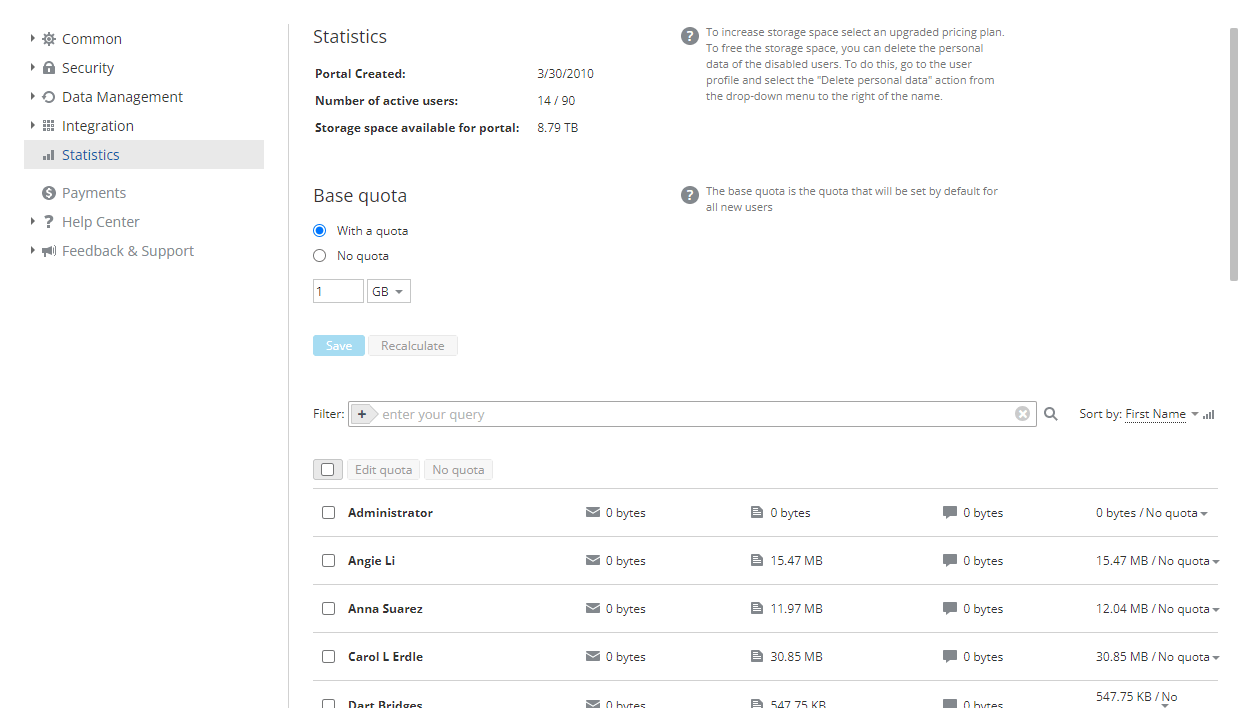
Managing memory quota
You can enable and set the base memory quota that will be applied to all new users:
- Select the With quota radio button.
- Set the desired value in the input field and choose the unit of measure from the drop-down list (bytes, Kb, Mb, Gb, Tb).
- Click Save.
To disable the quota, use the No quota option. The Recalculate button is used to recalculate the space used by users.
The user list below allows you to set the quota for several users or for a certain user separately. To easily find users, you can filter the list by email (Active, Pending), by type (Administrator, User, Guest), or by group. It is also possible to sort the list by first or last name or enter the necessary name in the search field.
To set the quota for several users:
- Check the necessary users in the list.
- Click the Edit quota button above.
- Set the desired value in the input field and choose the unit of measure from the drop-down list (bytes, Kb, Mb, Gb, Tb).
- Click the checkmark button to save the settings.
To set the quota for a certain user:
- Click the No quota section to the right of the user name.
- Select the Edit quota option from the drop-down list.
- Set the desired value in the input field and choose the unit of measure from the drop-down list (bytes, Kb, Mb, Gb, Tb).
- Click the checkmark button to save the settings.
Watch video
ONLYOFFICE Workspace 12.5.
ONLYOFFICE Workspace 12.5 makes your work even more secure and productive: enhanced authentication security, folder sharing via external links, Dark mode, Improved mail, Impersonation.