- Home
- Workspace
- Administration
- Using Control Panel
- Switching to HTTPS using Control Panel
Switching to HTTPS using Control Panel
Introduction
Control Panel offers you the possibility to quickly and easily switch your portal to the secure HTTPS protocol.
There are two ways to enable HTTPS for your portal via the Control Panel interface:
- If you don't have any SSL certificates, you can generate a new signed certificate with one click. The Control Panel uses the letsencrypt.org service to generate the CA-signed certificates.
- If you have an existing private key generated on your server and a public key certificate created on its base (self-signed or issued by a Certification Authority), you can simply upload them in the Control Panel.
A self-signed certificate is signed by the same person who creates it. Such a certificate can be created using the OpenSSL toolkit, for example. Although self-signed certificates ensure a sufficient security level, they may cause some issues. E.g., when you access your portal, a security warning appears in a browser informing you that the certificate cannot be verified. They are also considered more vulnerable to the man-in-the-middle attacks. It's better to use self-signed certificates for testing purposes or on a server that can only be accessed from your local network.
A CA-signed certificate is signed by a trusted third party (Certification Authority, CA). Such certificates can be acquired from any SSL certificate provider you like. In most cases, to do that you need to generate a private key and CSR (Certificate Signing Request) using any preferred tool (OpenSSL, for example), then send the CSR to a Certificate Authority who will verify your identity and issue a signed certificate. In the case of such a certificate usage, the Certificate Authority verifies that the certificate is valid, so no security warnings will be displayed. Besides, a higher security level will be enabled for sensitive data.
To access Control Panel, sign in to your portal and click the 'Control Panel' link on the Start Page. Alternatively, you can go to the portal 'Settings' and click the 'Control Panel' link on the left-side panel.
Generate a new certificate
To generate a new certificate:
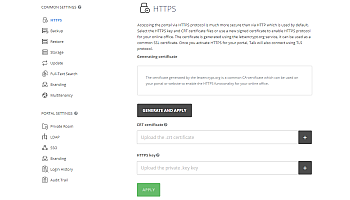
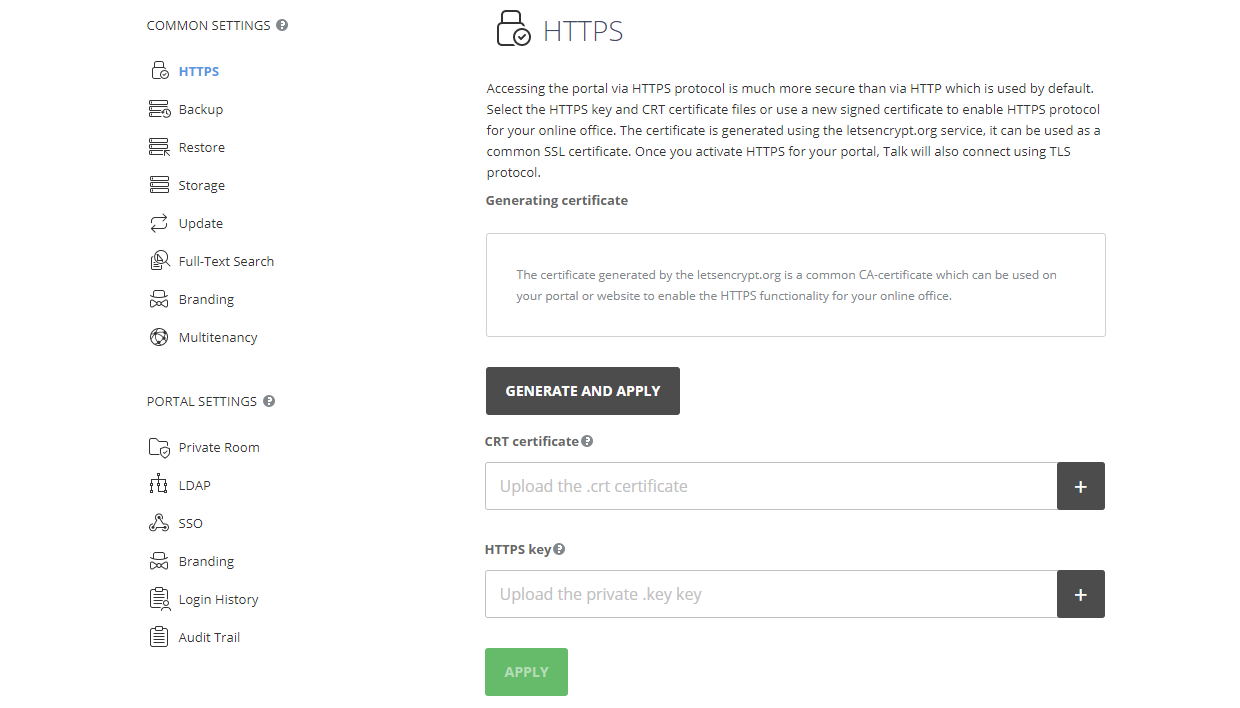
- Open the HTTPS page in the COMMON SETTINGS section on the left sidebar.
- Click the GENERATE AND APPLY button. A popup message box will appear informing you that the certificate and private key are successfully generated.
- After that your Control Panel and portal will be restarted and become unavailable during this process. It can take up to 5 minutes. Once the certificate installation process is over, your portal will be available over HTTPS.
To remove the installed certificate, use the DELETE button.
Upload an existing certificate and private key
To use an existing .crt certificate and private .key key:
- Open the HTTPS page in the COMMON SETTINGS section on the left sidebar.
- Click the Plus button next to the CRT certificate field and select your .crt certificate to upload it.
- Click the Plus button next to the HTTPS key field and select your private .key key to upload it.
Before uploading, please make sure that the private key is not encrypted. If you have a password-protected .key file, you will need to decrypt it first.
- Once the .crt and .key files are uploaded, click the APPLY button at the bottom of the page.
- After that your Control Panel and portal will be restarted and become unavailable during this process. It can take up to 5 minutes. Once the certificate installation process is over, your portal will be available over HTTPS. The domain name that your certificate was issued for is now displayed in the Generated on domain section of the HTTPS page in the Control Panel.
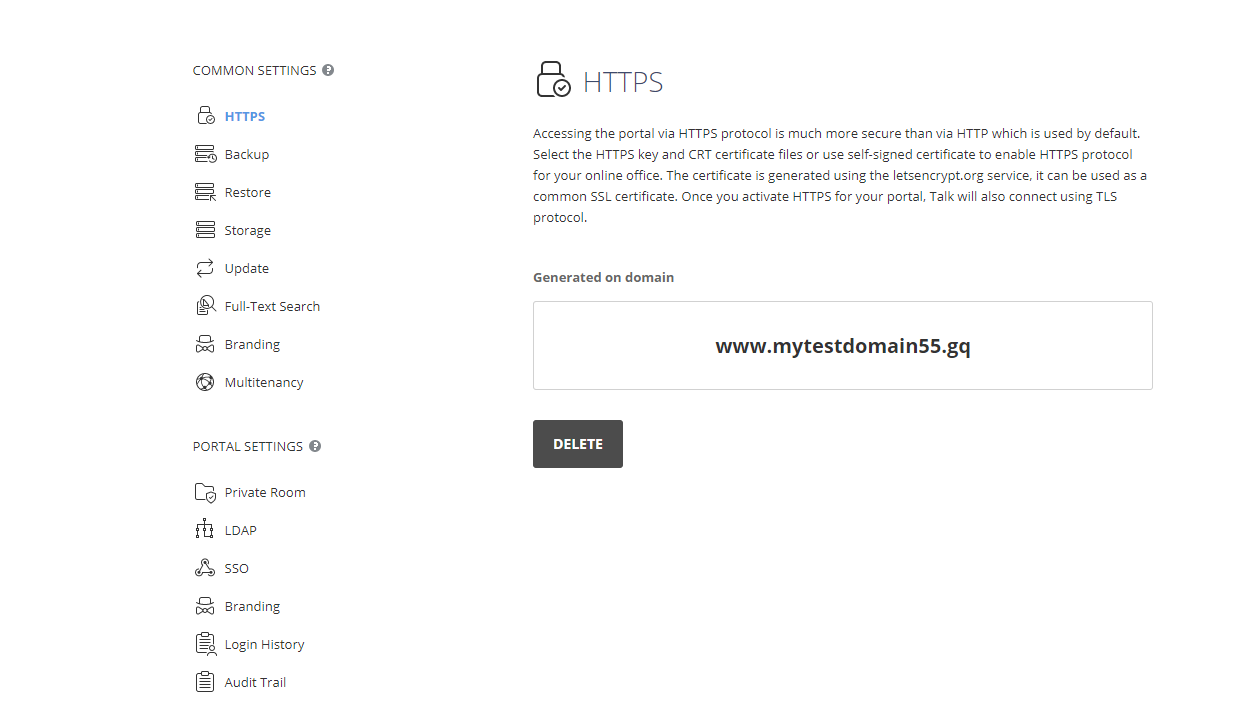
To remove the installed certificate, use the DELETE button.